Key takeaways
-
Privacy coins are just a step in a broader laundering pipeline after hacks. They serve as a temporary black box to disrupt traceability.
-
Hackers typically move funds through consolidation, obfuscation and chain hopping and only then introduce privacy layers before attempting to cash out.
-
Privacy coins are most useful immediately after a hack because they reduce onchain visibility, delay blacklisting and help break attribution links.
-
Enforcement actions against mixers and other laundering tools often shift illicit flows toward alternative routes, including privacy coins.
After crypto hacks occur, scammers often move stolen funds through privacy-focused cryptocurrencies. While this has created a perception of hackers preferring privacy coins, these assets function as a specialized “black box” within a larger laundering pipeline. To understand why privacy coins show up after hacks, you need to take into account the process of crypto laundering.
This article explores how funds move post-hack and what makes privacy coins so useful for scammers. It examines emerging laundering methods, limitations of privacy coins like Monero (XMR) and Zcash (ZEC) as laundering tools, legitimate uses of privacy technologies and why regulators need to balance innovation with the need to curb laundering.
How funds flow after a hack
Following a hack, scammers don’t usually send stolen assets directly to an exchange for immediate liquidation; instead, they follow a deliberate, multi-stage process to obscure the trail and slow down the inquiry:
-
Consolidation: Funds from multiple victim addresses are transferred to a smaller number of wallets.
-
Obfuscation: Assets are shuffled through chains of intermediary crypto wallets, often with the help of crypto mixers.
-
Chain-hopping: Funds are bridged or swapped to different blockchains, breaking continuity within any single network’s tracking tools.
-
Privacy layer: A portion of funds is converted into privacy-focused assets or routed through privacy-preserving protocols.
-
Cash-out: Assets are eventually exchanged for more liquid cryptocurrencies or fiat through centralized exchanges, over-the-counter (OTC) desks or peer-to-peer (P2P) channels.
Privacy coins usually enter the stage in steps four or five, blurring the traceability of lost funds even more after earlier steps have already complicated the onchain history.

Why privacy coins are attractive for scammers right after a hack
Privacy coins offer specific advantages right at the time when scammers are most vulnerable, immediately after the theft.
Reduced onchain visibility
Unlike transparent blockchains, where the sender and receiver and transaction amounts remain fully auditable, privacy-focused systems deliberately hide these details. Once funds move into such networks, standard blockchain analytics lose much of their efficacy.
In the aftermath of the theft, scammers try to delay identification or evade automated address blacklisting by exchanges and services. The sudden drop in visibility is particularly valuable in the critical days after theft when monitoring is most intense.
Breaking attribution chains
Scammers tend not to move directly from hacked assets into privacy coins. They typically use multiple techniques, swaps, cross-chain bridges and intermediary wallets before introducing a privacy layer.
This multi-step approach makes it significantly harder to connect the final output back to the original hack. Privacy coins act more as a strategic firebreak in the attribution process than as a standalone laundering tool.
Negotiating power in OTC and P2P markets
Many laundering paths involve informal OTC brokers or P2P traders who operate outside extensively regulated exchanges.
Using privacy-enhanced assets reduces the information counterparties have about the funds’ origin. This can simplify negotiations, lower the perceived risk of mid-transaction freezes and improve the attacker’s leverage in less transparent markets.
Did you know? Several early ransomware groups originally demanded payment in Bitcoin (BTC) but later switched to privacy coins only after exchanges began cooperating more closely with law enforcement on address blacklisting.
The mixer squeeze and evolving methods of laundering
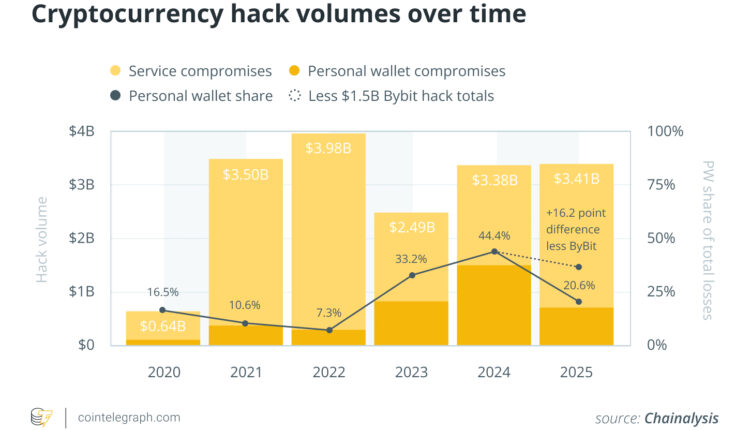
One reason privacy coins appear more frequently in specific time frames is enforcement pressure on other laundering tools. When law enforcement targets particular mixers, bridges or high-risk exchanges, illicit funds simply move to other channels. This shift results in the diversification of laundering routes across various blockchains, swapping platforms and privacy-focused networks.
When scammers perceive one laundering route as risky, alternative routes experience higher volumes. Privacy coins gain from this dynamic, as they offer inherent transaction obfuscation, independent of third-party services.
Limitations of privacy coins as a laundering tool
Privacy features notwithstanding, most large-scale hacks still involve extensive use of BTC, Ether (ETH) and stablecoins at later stages. The reason is straightforward: Liquidity and exit options are important.
Privacy coins generally exhibit:
These factors complicate the conversion of substantial amounts of crypto to fiat currency without drawing scrutiny. Therefore, scammers use privacy coins briefly before reverting to more liquid assets prior to final withdrawal.
Successful laundering involves integration of privacy-enhancing tools with high-liquidity assets, tailored to each phase of the process.
Did you know? Some darknet marketplaces now list prices in Monero by default, even if they still accept Bitcoin, because vendors prefer not to reveal their income patterns or customer volume.
Behavioral trends in asset laundering
While tactical specifics vary, blockchain analysts generally identify several high-level “red flags” in illicit fund flows:
-
Layering and consolidation: Rapid dispersal of assets across a vast network of wallets, followed by strategic reaggregation to simplify the final exit.
-
Chain hopping: Moving assets across multiple blockchains to break the deterministic link of a single ledger, often sandwiching privacy-enhancing protocols.
-
Strategic latency: Allowing funds to remain dormant for extended periods to bypass the window of heightened public and regulatory scrutiny.
-
Direct-to-fiat workarounds: Preferring OTC brokers for the final liquidation to avoid the robust monitoring systems of major exchanges.
-
Hybrid privacy: Using privacy-centric coins as a specialized tool within a broader laundering strategy, rather than as a total replacement for mainstream assets.
Contours of anonymity: Why traceability persists
Despite the hurdles created by privacy-preserving technologies, investigators continue to secure wins by targeting the edges of the ecosystem. Progress is typically made through:
-
Regulated gateways: Forcing interactions with exchanges that mandate rigorous identity verification
-
Human networks: Targeting the physical infrastructure of money-mule syndicates and OTC desks
-
Off-chain intelligence: Leveraging traditional surveillance, confidential informants and Suspicious Activity Reports (SARs)
-
Operational friction: Exploiting mistakes made by the perpetrator that link their digital footprint to a real-world identity.
Privacy coins increase the complexity and cost of an investigation, but they cannot fully insulate scammers from the combined pressure of forensic analysis and traditional law enforcement.
Did you know? Blockchain analytics firms often focus less on privacy coins themselves and more on tracing how funds enter and exit them since those boundary points offer the most reliable investigative signals.
Reality of legitimate use for privacy-enhancing technologies
It is essential to distinguish between the technology itself and its potential criminal applications. Privacy-focused financial tools, such as certain cryptocurrencies or mixers, serve valid purposes, including:
-
Safeguarding the confidentiality of commercial transactions, which includes protecting trade secrets or competitive business dealings
-
Shielding individuals from surveillance or monitoring in hostile environments
-
Reducing the risk of targeted theft by limiting public visibility of personal wealth.
Regulatory scrutiny isn’t triggered by the mere existence of privacy features, but when they are used for illicit activity, such as ransomware payments, hacking proceeds, sanctions evasion or darknet marketplaces.
This key distinction makes effective policymaking difficult. Broad prohibitions risk curtailing lawful financial privacy for ordinary users and businesses while often failing to halt criminal networks that shift to alternative methods.
Balancing act of regulators
For cryptocurrency exchanges, the recurring appearance of privacy coins in post-hack laundering flows intensifies the need to:
-
Enhance transaction monitoring and risk assessment
-
Reduce exposure to high-risk inflows
-
Strengthen compliance with cross-border Travel Rule requirements and other jurisdictional standards.
For policymakers, it underscores a persistent challenge: Criminal actors adapt more quickly than rigid regulations can evolve. Efforts to crack down on one tool often displace activity to others, turning money laundering into a dynamic, moving target rather than a problem that can be fully eradicated.
Cointelegraph maintains full editorial independence. The selection, commissioning and publication of Features and Magazine content are not influenced by advertisers, partners or commercial relationships.